Fast track penetration testing
 By typing sessions --i 1 you can now access the pwned machine using the first vulnerability or replace the 1 with a 2, 3, or 4 to use one of the other three vulnerabilities, and drop into a meterpreter prompt. Then navigate to your home directory and download Metasploit itself. Once the process has completed we are ready to get testing. Since they are quick and easy to use they can be used by unskilled hackers or script kiddies - which makes it all the more important that you run these tools yourself so you can fix any vulnerabilities you find before they are exploited by others. SET February 18, ports Exploitation Tools , Information Gathering. Information security professional, analyst, speaker and technical writer.
By typing sessions --i 1 you can now access the pwned machine using the first vulnerability or replace the 1 with a 2, 3, or 4 to use one of the other three vulnerabilities, and drop into a meterpreter prompt. Then navigate to your home directory and download Metasploit itself. Once the process has completed we are ready to get testing. Since they are quick and easy to use they can be used by unskilled hackers or script kiddies - which makes it all the more important that you run these tools yourself so you can fix any vulnerabilities you find before they are exploited by others. SET February 18, ports Exploitation Tools , Information Gathering. Information security professional, analyst, speaker and technical writer.





The Ultimate Penetration Testing Command Cheat Sheet for Linux
 Network Security Training Package. Hands-on Advanced Application Security: Thanks for your registration, follow us on our social networks to keep up-to-date. RM 1, On Site: For instance, within the Metasploit framework discussed in the next section , you can actually build a database of hosts and targets using NMAP scans. List Scan — simply list targets to scan.
Network Security Training Package. Hands-on Advanced Application Security: Thanks for your registration, follow us on our social networks to keep up-to-date. RM 1, On Site: For instance, within the Metasploit framework discussed in the next section , you can actually build a database of hosts and targets using NMAP scans. List Scan — simply list targets to scan.

The Ultimate Penetration Testing Command Cheat Sheet for Linux
Guess OS more aggressively. Receive special group discounts and save on travel expenses and time out of the office with courses at your site or office. When extracting the tarball, run the setup. For more information on Fast-Track, visit Fast-Track at www.





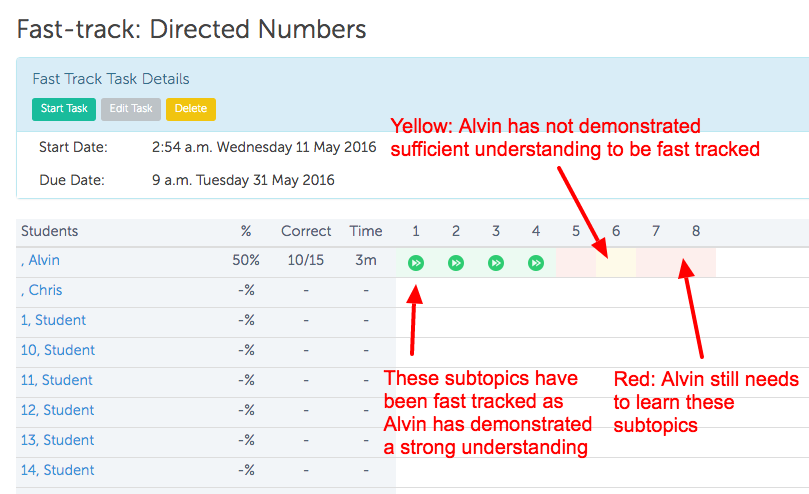
Automate Pen Testing with Fast-Track Client-Side Attacks
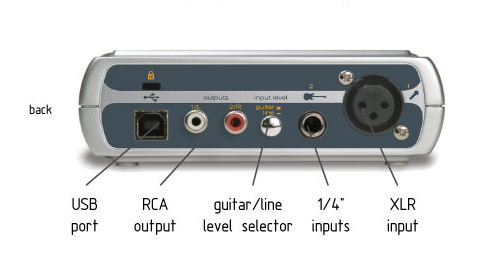
Description: To do this is starts a Web server on the penetration testing machine running Fast-Track, and imports all of Metasploit's client-side attacks as well as Fast-Track's own. Instead, you want to use the netstat command. Fast mode — Scan fewer ports than the default scan. Metasploit 3, SQLite, PYMSSQL, FreeTDS, Pexpect, ClientForms, Beautiful Soup, and Psycho.
Views: 1383
Date: 13.06.2015
Favorited: 5


































User Comments
Post a comment
Comment: